If you are security conscious and want to find an easy way to determine what aspects of your server setup are presently vulnerable to known
If you want to harden the security of your Plesk VPS, there are a couple of things you can do from disabling non-essential apache modules
The voter access decision strategy can be set in your Symfony2 app/config/security.yml. You have the choice of 3 approaches (Unanimous, Affirmative, Consensus). Set your strategy to
I needing to setup a staging environment that more or less emulates the platform of your deployment system, i needed to setup a LAMP stack
So i had an issue that i am still somewhat unsure of the cause, though i suspect the culprit was an upgrade to a newer
Quick cheat sheet for referencing. Tags are a way to bookmark a particular version of your git repository for future referencing. Use them to bookmark
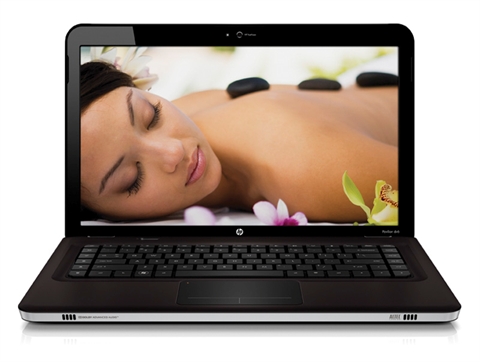
New laptop! YAY. So i decided i wanted a new machine to run linux on as its a bit tiresome running Linux in a VM,